How to Integrate Data Destruction Techniques right into Your Cyber Security Method
Wiki Article
The Relevance of Effective Data Damage Practices in Safeguarding Sensitive Details and Ensuring Computer Safety And Security
In an era where information violations are progressively common, the value of effective information damage practices can not be overstated. Organizations face significant threats when delicate info is improperly disposed of, possibly resulting in unauthorized accessibility and serious economic repercussions. Executing durable information devastation methods not just mitigates these threats yet also straightens with legal compliance demands, ensuring that companies support their online reputation and foster customer depend on. The inquiry continues to be: what certain techniques can be used to boost these techniques, and exactly how can organizations successfully integrate them into their overall cybersecurity structure?Recognizing Information Devastation
Understanding information devastation is critical in today's electronic landscape, where sensitive details can quickly be endangered. Efficient information destruction entails not just removing files however guaranteeing that information is irretrievable through comprehensive methods. This procedure is essential for companies that deal with personal customer info, intellectual residential property, or interior files, as any breach can result in serious financial and reputational consequences.
Information destruction encompasses different strategies, including shredding physical media, degaussing magnetic storage space devices, and employing software-based solutions that overwrite information numerous times. Each technique offers a certain objective and must align with the sensitivity of the info being thrown away. For instance, physical damage is frequently favored for hard disks containing highly private data, while software program approaches might be adequate for less delicate details.
Additionally, sticking to sector criteria and regulations, such as the General Information Security Policy (GDPR) or the Medical Insurance Portability and Responsibility Act (HIPAA), is imperative for compliance and to mitigate lawful dangers. Organizations should establish a robust data damage plan, train employees on ideal practices, and on a regular basis examine their procedures to make sure that all delicate details is dealt with safely and successfully.
Threats of Inadequate Practices
Insufficient data destruction techniques expose companies to substantial threats that can have significant consequences. When delicate information is not correctly gotten rid of, it stays susceptible to unapproved gain access to, which can lead to information violations and identification burglary. Such events not just compromise the safety and security of individuals but additionally stain the company's online reputation, causing a loss of consumer trust fund and potential financial consequences.Additionally, governing compliance is progressively rigid in lots of sectors. Failing to comply with information destruction regulations can lead to hefty penalties and lawsuits versus companies. These penalties can strain funds and draw away interest from core company procedures.
Furthermore, the abuse of recurring information can bring about intellectual building burglary or company reconnaissance, jeopardizing affordable benefits (data destruction). The impact of inadequate data damage prolongs beyond immediate financial losses; it can additionally result in long-lasting damage to brand integrity and market position

Organizations must identify that information safety is not solely concerning stopping breaches; it likewise includes the responsible management of data throughout its lifecycle. Disregarding reliable information damage procedures can have tragic effects, highlighting the need for robust measures to alleviate these risks.
Finest Practices for Information Damage
Executing efficient information damage methods is crucial for guarding sensitive details and keeping conformity with regulatory criteria. Organizations must embrace a multi-faceted strategy to ensure that information is irretrievable, consequently avoiding unapproved access and possible breaches.First, data need to be categorized based on level of sensitivity, allowing organizations to use ideal devastation techniques customized to the level of risk. For digital data, making use of software-based data-wiping devices that comply with market standards can efficiently overwrite existing information. Physical damage techniques, such as shredding or degaussing, are important for gadgets that save delicate details, visite site ensuring full obliteration.
Developing a clear data retention policy is essential, outlining for how long different kinds of details need to be maintained before devastation. Routine audits of data storage space systems are also essential to recognize outdated or unnecessary information requiring elimination.
Furthermore, training staff members on the significance of information devastation and the certain protocols to adhere to fosters a culture of protection within the company. Ultimately, maintaining documentation of data devastation refines gives accountability and sustains conformity with outside guidelines and interior policies. By sticking to these best techniques, organizations can considerably minimize the threats linked with data direct exposure.
Legal and Compliance Factors To Consider

Failing to adhere to these guidelines can result in extreme penalties, including significant penalties and reputational damage. Organizations should implement a robust information devastation policy that straightens with these legal structures and gives clear guidelines on the proper techniques of information disposal, whether physical shredding or electronic wiping.
Furthermore, preserving documents of data devastation activities is necessary for showing compliance during audits or evaluations. By focusing on lawful and conformity factors to consider, here are the findings companies can boost their information security position and foster count on with stakeholders and customers, eventually adding to an extra safe and secure information monitoring setting.
Benefits of Effective Information Devastation
Reliable information destruction techniques extend beyond mere compliance; they provide significant advantages to companies that prioritize them. By making certain that delicate details is irretrievably damaged, companies minimize the threat of information violations and the prospective monetary consequences connected with them. This positive technique not just safeguards against unauthorized check this access but also boosts the total dependability of the company in the eyes of stakeholders and customers.Applying durable data destruction methods, such as physical destruction of storage space tools or sophisticated data cleaning methods, contributes to the conditioning of an organization's cybersecurity stance. data destruction. It minimizes the probability of intellectual residential or commercial property burglary and protects exclusive details, therefore maintaining an one-upmanship in the marketplace

Verdict
In conclusion, effective data damage techniques are essential for protecting delicate details and boosting overall computer safety. By carrying out thorough methods such as shredding, degaussing, and software application overwriting, companies can reduce the threats linked with unauthorized access and data breaches. Adherence to governing criteria, consisting of GDPR and HIPAA, more enhances conformity and secures versus lawful consequences. Inevitably, a dedication to robust data destruction strategies fosters a society of duty, consequently enhancing an organization's cybersecurity position and maintaining client count on.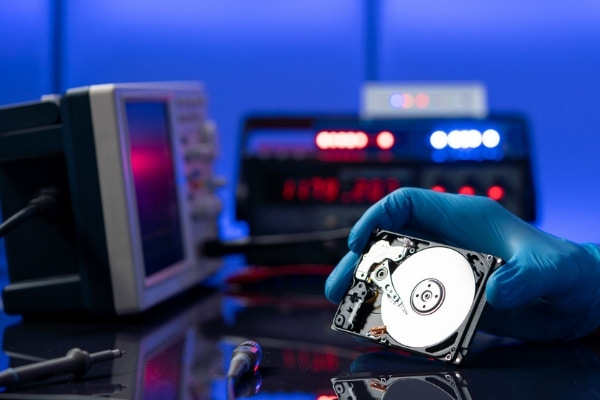
Report this wiki page